Challenge and Password
From Combat Training of the Individual Soldier and Patrolling, July 1967
- The Challenge and Password
- The enemy may come from any direction, especially when you are engaged in counter guerrilla operations. Keep watch in all directions. Halt and identify personnel before they are close enough to be a danger to you (fig. 12). This precaution is even more important at night and during periods of poor visibility such as heavy fog.
- In most cases, identity is established by
proper use of the challenge and password. When
you see or hear someone approaching, and do
not recognize him as friendly and authorized to
pass; call, "Halt!" Speak clearly and just
loudly enough to be distinctly heard. Keep him
covered and do not expose yourself. When he
halts, ask in a low, clear voice, "Who is
there?"
He should reply in a low, clear voice, giving the
answer which best identifies him. For example, "Sergeant Cleary,
second squad." or "Private
Willard, messenger." You then say, "Advance
to be recognized." Continue
to keep him covered without exposing yourself. Halt him 2 or 3
meters from your position. In a low, clear voice
give him the challenge; for example, "Boston."
He should answer with the password; for example, "Beans." If
you are not completely satisfied, require him to produce identification
or question him further. Ask questions only a
friendly person would be likely to know (FM
22-6, STANAG No. 2042).

- When a group approaches and is halted, the
leader should answer for the group. For example, "Friendly
patrol" or "Friendly
wire team." You then say, "Advance
one man to be recognized." When the challenge and password
have been given and identity is established, the
other members of the group must also be identified. Tins can be done
in two ways. Your commander should prescribe the manner to be
used in your unit.
- The leader can vouch for the others and pass them to the flank of your position. This method reduces movement and noise at your position and helps prevent revealing your location to the enemy.
- The leader, or his representative, can
identify each man as he passes, notifying you when the last man
has passed.

- You may be approached by a soldier, or a group, who does not know the challenge and password. This could be the case of a soldier, separated from a patrol sent out by a distant unit, who has found his way to your area. This could also be the case of soldiers who were isolated in the enemy area. and have evaded capture and reached your area. These evaders may even be in civilian clothes. If such personnel can produce satisfactory identification, detain them nearby where they will not be exposed, and contact your commander. If they cannot satisfactorily identify themselves, keep them covered, at a safe distance from your position, and contact your commander.
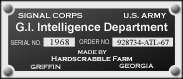
- The challenge and password are changed every 24 hours (usually at 1200 hours). Be sure you know the current ones. If you do not receive the new words, make a request for them.
- The regular challenge and password should not be used outside friendly areas. Patrols, for example, should use a different challenge and password for recognition within patrols and between patrols operating in the same general area. Words can be used in the same manner as the regular challenge and password or a numbers system can be used. For example, the challenge is a number; the password is the number which, added to the challenge, totals a prearranged odd number. If the prearranged number is 13, the challenge is any number between 1 and 12. The password is the number which, added to the challenge, equals 13. Only odd numbers should be used as the prearranged total. If even numbers are used, such as 10, someone may challenge with 5; an enemy, upon being challenged, may repeat the number spoken and be passed as having been identified.
- The principle to remember is that a means
of recognition must be established and must be
properly used.